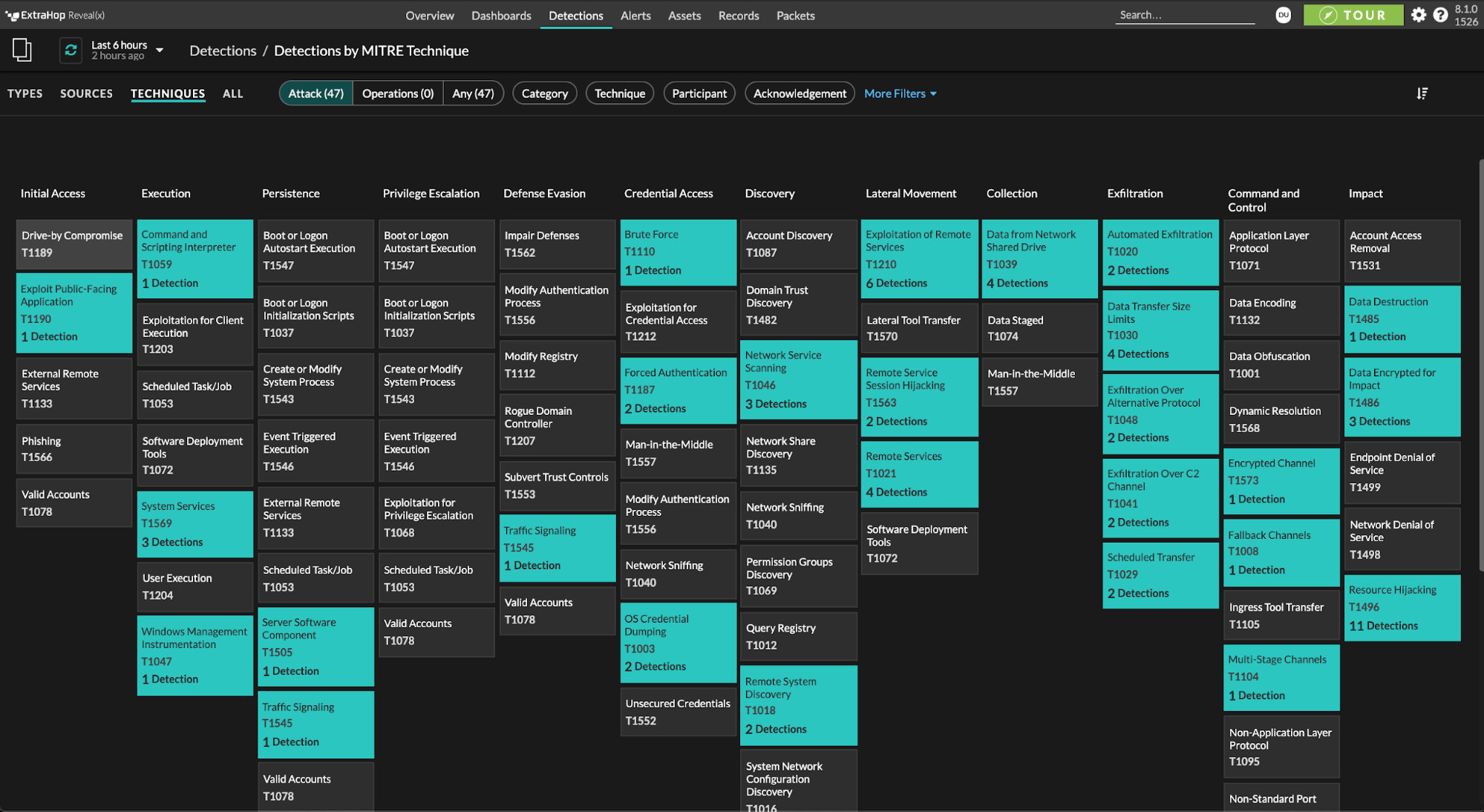
The MITRE ATT&CK framework has rapidly become the go-to lens through which security operations teams view their ability to detect attacker tactics, techniques, and procedures (TTPs). The ATT&CK framework comprises 191 techniques, and 385 sub techniques (and counting) across fourteen tactic categories—starting with reconnaissance and proceeding through initial compromise, maintaining persistence, defense evasion, and finally impact—spanning the course of a full cyberattack campaign.
When enterprise SecOps teams use MITRE ATT&CK to understand the behavior they observe in their own environment, they gain a clearer view of which attack tactics they're able to detect and which might fly under the radar or evade their defenses and eventually lead to a breach. Understanding these gaps in their defenses makes it easier to decide where to invest security budgets, and how to update policies and procedures to assure strong, effective defenses.
Currently, the MITRE ATT&CK framework is heavily weighted towards endpoint-centric attack tactics. Detection and investigation of a large percentage of the TTPs cataloged in the framework require visibility into files and processes on individual endpoints. Endpoint detection and response (EDR) is an area of heavy investment for security teams, and it makes sense that they want industry standards and frameworks to both scrutinize and validate the effectiveness of their programs. However, many crucial TTPs, especially in the later stages of an attack campaign, are easier to detect on the network. Automatically analyzing and correlating both data sources makes it easier for analysts to make fast, informed decisions and respond precisely to urgent threats.
Learn How Integrated EDR and NDR Stop Breaches Faster
Network-Centric TTPs Can Make The Difference Between a Compromise and a Data Breach
When an attacker has compromised your network and begins to move laterally, hopping from endpoint to endpoint, you need to move quickly to prevent them from maintaining a foothold, staging, and eventually exfiltrating critical data in a way that represents a potentially irreversible data breach. Many enterprises have less visibility into internal lateral movement than they do ingress and egress. Attackers that get past the perimeter have an easier time staying stealthy and meeting high-impact attack objectives.
Defense Evasion
If an attacker is inside the environment, that means they've likely already circumvented some defenses. A few common ways to do this would be:
- Assessing which endpoints are monitored by agents or antivirus, and avoiding them
- Deleting or altering activity logs to mask suspicious behavior
- Hijacking or injecting attack behavior into unmonitored processes to evade endpoint security
- Stealing valid credentials and using them for unauthorized purposes
Many times, endpoint security, next-gen antivirus, or firewalls will catch these tactics if they affect perimeter-based or internet-facing devices. But attackers know it only has to work once for them to get the toehold they need, so they keep trying and keep developing new tactics for bypassing these security mechanisms. Software supply chain attacks, such as the SolarWinds SUNBURST attack, or the abuse of a vulnerability in the Kaseya VSA management software, are an increasingly popular method to evade perimeter security altogether.
In all of these cases, the attacker buys themself time to expand their footprint in the target environment. Security teams that have the ability to detect what happens after these behaviors are in a much better position to reduce dwell time (the amount of time the attacker has before being detected) to achieve their goals of stealing or destroying data, or distributing and detonating ransomware.
This is where network detection and response (NDR) comes in.
The Asymmetric Battle and How Covert Defenses Can Help
Why are attackers able to circumvent established security mechanisms so effectively, and what can a savvy security team do next? There are two issues that security teams should be aware of:
One is the asymmetry inherent in the relationship between attackers and defenders. An attacker only has to get past the perimeter once to make their job much, much easier. Few, if any, companies have the same level of security visibility inside their environment as they do at the edge—although that's changing.
The second is that perimeter and endpoint security mechanisms are visible to the attacker. A quick scan of a compromised laptop can reveal whether or not that laptop has an endpoint protection agent on it, and whether its activity is being logged. If an attacker knows which defenses lie in wait for them, they can plan ahead and disable those defenses, or just target unmanaged and unsecured devices exclusively.
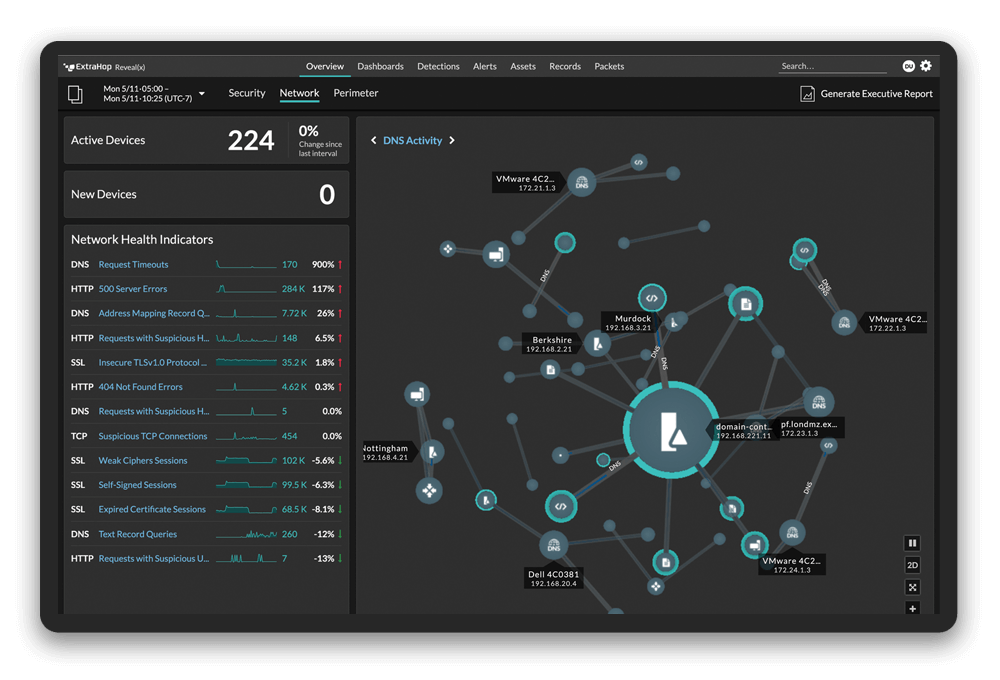
Network detection and response addresses both of these challenges. Because NDR platforms observe all communications across the inside of a network, in the east-west corridor, they are able to detect unusual lateral movement, suspicious behavior by users, and new, unauthorized devices as soon as they connect. Because NDR platforms ingest data passively, an attacker has no way of knowing whether their behavior is being watched, nor any mechanism for altering the configuration of the observation. They may attempt to evade detection by encrypting their traffic, but that traffic can be decrypted for analysis, or simply blocked if unauthorized, out-of-policy encryption schemes are detected.
These characteristics make NDR a fantastic mechanism for detecting and investigating the kinds of behaviors that attackers do after they bypass perimeter-focused defenses.
Webinar: How XDR Gets Real: Stop Advanced Threats with ExtraHop and Crowdstrike
What Makes Some MITRE ATT&CK TTPs Network-Centric?
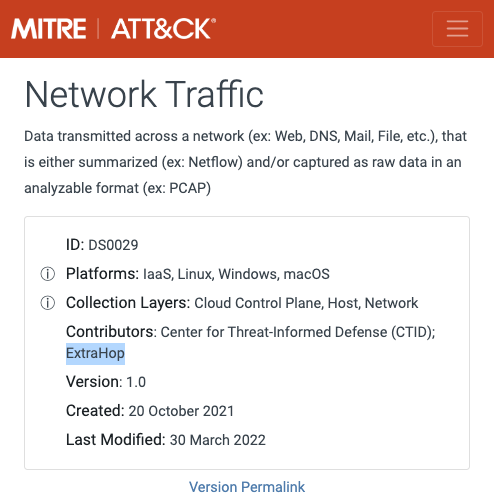
Each MITRE ATT&CK tactic listing includes a list of data sources that are useful for determining the best way to detect and investigate that particular tactic. Looking for TTPs that list network traffic content, network traffic flow, or network connection creation is a good way to identify which TTPs are better to detect and investigate using network traffic. Examples include:
- Remote Access Tools (T1219)
- Remote File Copy (T1105)
- DCShadow (T1207)
- And dozens more
While network-centric TTPs appear in all 12 of the main Technique Categories in the MITRE ATT&CK Framework, they are more heavily concentrated in certain categories, including:
- Lateral Movement
- Credential Access
- Command & Control
- Data Exfiltration
The reason for this is, once an attacker has compromised an environment, they have likely already evaded other safeguards in place to prevent them from doing so. At this point, the attacker still has a long way to go before completing their objective. Well-equipped defenders can still stop the breach, as long as they have the right tools!
Because network detection and response consumes data passively and is not visible to the attacker, they cannot evade or disable it in the same way. Security teams can rely on NDR as a covert line of defense that will continue to be effective even when an attacker believes that they're in the clear.
EDR and activity logging from a SIEM solution are both vital tools for any security operations team. Both can catch many of the TTPs attackers attempt in the early stages of an attack campaign or behaviors that manifest on-host without generating network activity. This includes common malware behaviors such as process spawning, directory traversal, and on-host privilege escalation. For the latter stages of an attack, NDR is the best approach to ensure that a compromise doesn't progress into a full-on data breach. Using an integrated set of best-of-breed NDR, EDR, and SIEM solutions is the best approach to having the complete data set needed for thorough detection and response.